It would appear that more and more companies and home users are becoming victim to bad actors intruding on their network. Weather it be a targeted attack or drive by malware, network security is a hot topic in today’s IT landscape. In this article I will describe how you can build a low cost Honey Pot that can help alert you to an intrusion before its too late.
What is a Honey Pot?
In simple terms a Honey Pot is a device on your network that looks appetizing to a hacker. Like drawing a bear to a pot of honey. This device will advertise services that appear vulnerable and maybe draw an attacker in for further investigation. At a minimum it can simply be used as an internal “trip wire” to alert you someone poking around.
Why does a honey pot work?
 I’m Joe hacker and I have just installed malware on one of your employees workstations. I have quickly gained access and I am now able to execute code and commands. What is the first thing I’m going to do? If you said start poking around you would be correct. After I look for anything of value on my host computer I will quickly begin scanning the subnet looking for hosts that are alive. I will also begin mapping the network for services that are possibly vulnerable to attack. This is where the Honey Pot fits in. It has been patiently siting on your network waiting for someone to direct a packet of data in its direction and alert you to possible trouble.
I’m Joe hacker and I have just installed malware on one of your employees workstations. I have quickly gained access and I am now able to execute code and commands. What is the first thing I’m going to do? If you said start poking around you would be correct. After I look for anything of value on my host computer I will quickly begin scanning the subnet looking for hosts that are alive. I will also begin mapping the network for services that are possibly vulnerable to attack. This is where the Honey Pot fits in. It has been patiently siting on your network waiting for someone to direct a packet of data in its direction and alert you to possible trouble.
I’m in! How much does a honey pot cost?
If you’re a DIY type of network admin like me, you can get a Honey Pot up and running for under $80. If you are a multi million dollar corporation and have $5,000 to $10,000 to burn on Honey Pots stop reading now and google for THINKST CANARY .
As for the rest of us that don’t have an unlimited budget I am going to talk about two open source solutions that you can install on a Raspberry Pi and be up and running in just a few hours.
What hardware should I buy?
I personally like this CanaKit for $55 at Amazon It comes with just about  everything you need to get started.
everything you need to get started.
- Pi 3B+
- Power Supply
- Case
- Heat Sinks
- On / Off Switch
The only thing missing is an SD card. SD cards are so inexpensive now and you only need a 16GB card to get this project up and running.
If you don’t have a spare Micro SD card hanging around the house, you can pick this SanDisk Ultra card up for $7.00 at Amazon
pick this SanDisk Ultra card up for $7.00 at Amazon
Honey Pi -(Port Scan detector)
https://trustfoundry.net/honeypi-easy-honeypot-raspberry-pi/
Honey Pi runs on any Raspberry Pi 3 and is easy to get up and running in about 2 hours.
HoneyPi tries to keep it simple compared to other honeypots. HoneyPi only flags a few surefire triggers that would catch most attackers snooping around on an internal network:
-
-
- Port Scanning Activities
- FTP Connection Attempts
- Telnet Connection Attempts
- VNC Connection Attempts
-
OpenCanary –
https://xo.tc/installing-opencanary-on-a-raspberry-pi.html
OpenCanary is similar to Honey Pi, however it will allow you to advertise more vulnerable services and even capture user name and password the hacker uses to access the service.
It was a bit more difficult to setup, but if follow the instructions in the link you should have no issues getting the system up and running in a couple of hours.
Honey Pot Conclusion & Thoughts
My completed setup:
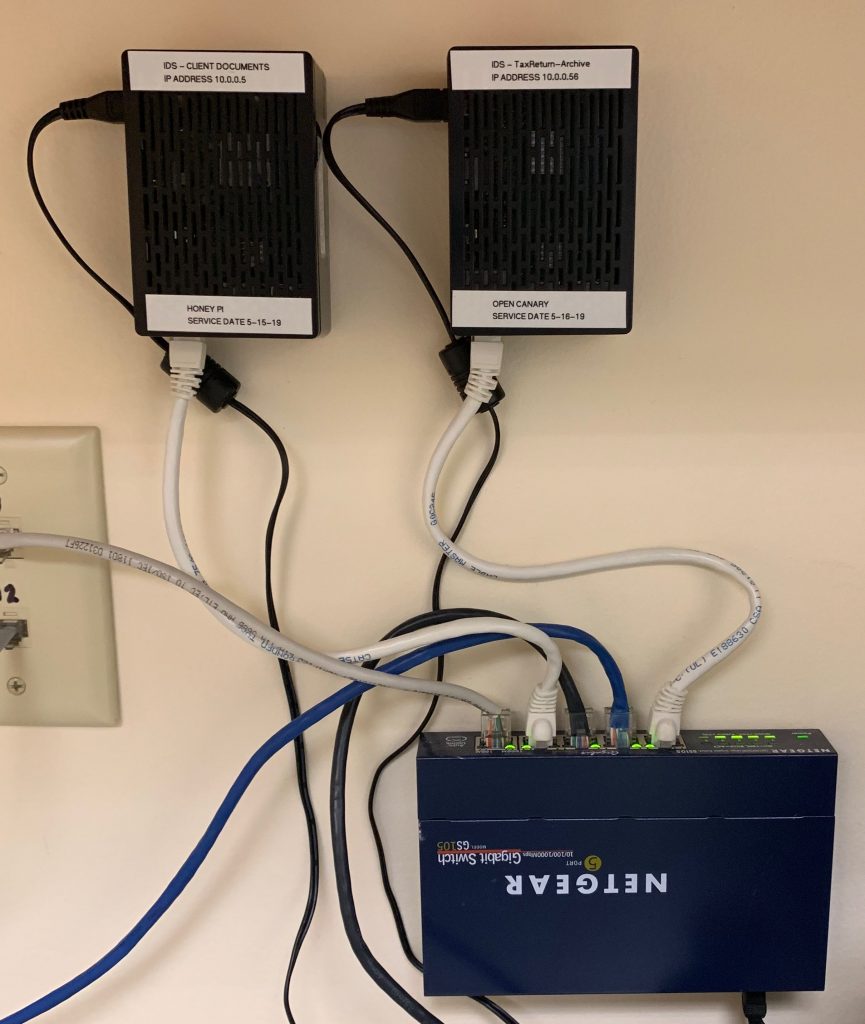
These devices can be used on the inside and outside of your network. For this project I’m concentrating on the inside. Lets assume someone has already infiltrated your network how would you know? It has also been said that 60% of network intrusions are employees or users that already have access to the internal network.
The software was easy to setup and get running. I did have some issues with email alerts but after a few google searches I was able to get everything sorted out.
One last thought, if you are going to build one of these devices you should have something on your network to monitor it and test is weekly. I wrote a BAT file (yes I’m old) and added it to a Windows task to attempt connections to these boxes on a weekly basis. This way I know they are still working.
RELATED TOPICS:
Motioneye Raspberry Pi Zero Security System
Turn On Your “Pi Hole” and say hello ad blocking on all your devices!
Thank you for reading my blog,
Joe
Don’t forget to visit my store:
www.GeekGearStore.com