A Blast from the Past: Free Sound Blaster Disk Images
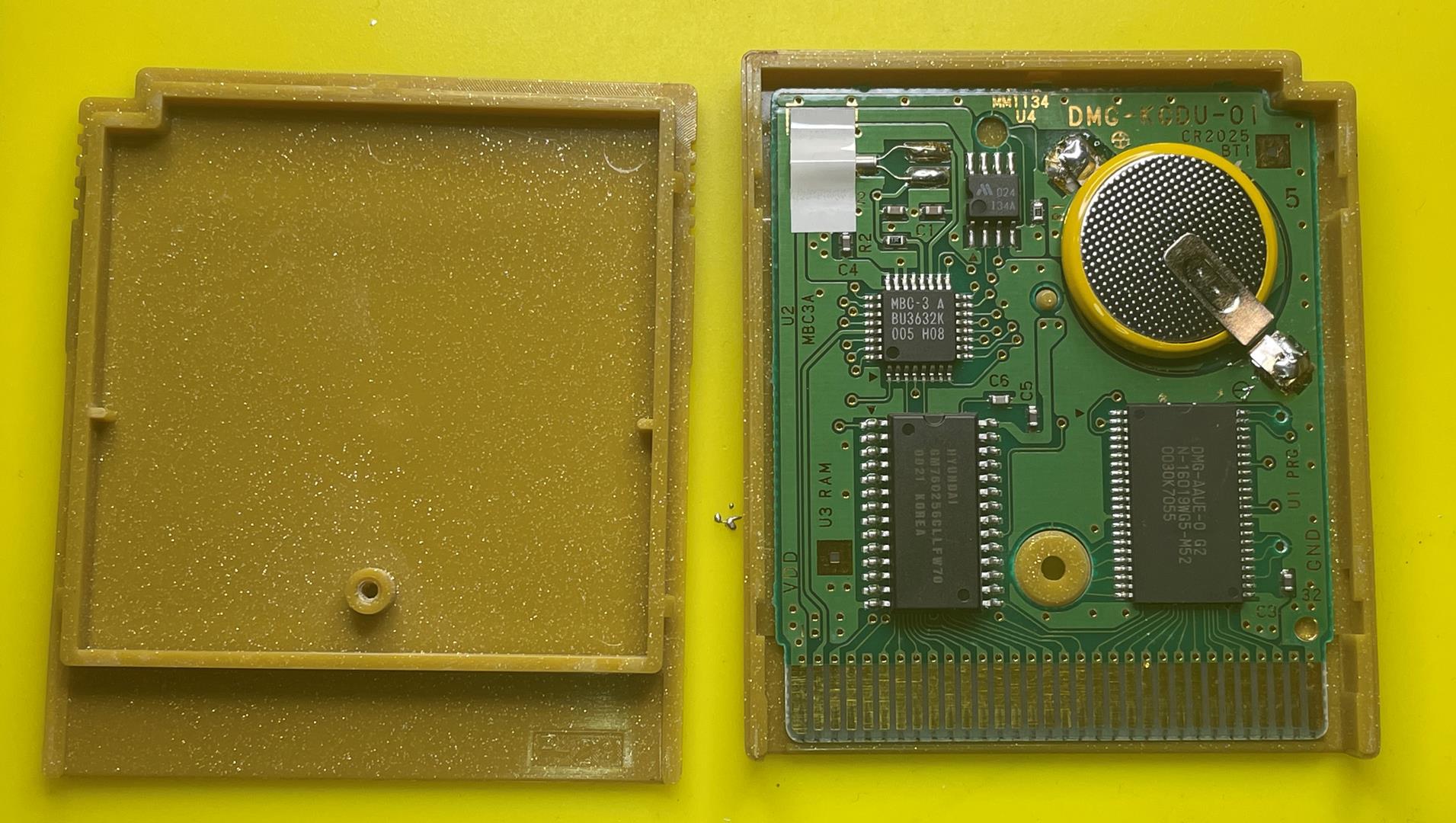
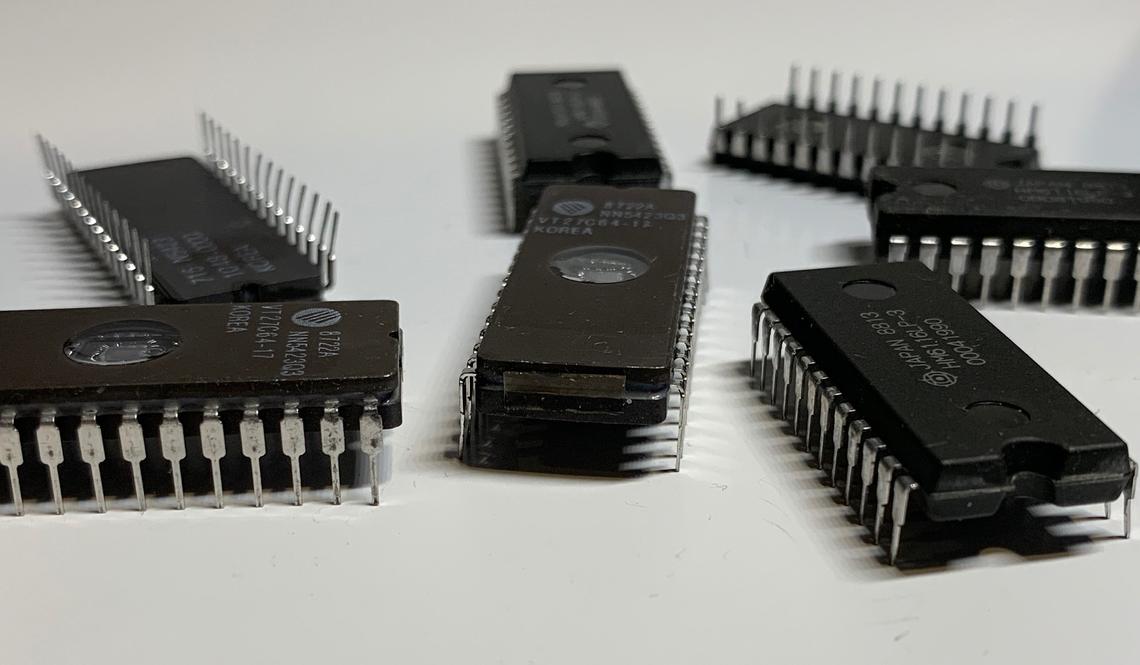
Get ready to take a trip down memory lane with the legendary Creative Labs Sound Blaster series. We’re excited to share that we have 10 vintage Sound Blaster floppy disks available, complete with their original disk images, for you to download and relive the nostalgic experience.
The Sound Blaster series revolutionized PC audio in the early 1990s, offering improved sound quality and effects capabilities. These iconic cards were a staple of any gamer’s or audio enthusiast’s setup back then, and we’re thrilled to offer a chance to revisit this bygone era.
Below are the disk images available for download:
- Sound Blaster Driver Disks 1-3 : Get the original drivers for your Sound
 Blaster card with these disks.
Blaster card with these disks.
Continue reading “Unleash Your Inner Retro Tech Enthusiast: Free Sound Blaster Disk Images”