If you’re as old as I am you may remember some of the auto body repair techniques of the late 70’s and early 80’s. It was an era of body fill ,shape and repair rather than today’s replace replace replace. While Bondo is still used in the automotive industry there are so many other uses for this stuff its ridiculous.
What I like most about Bondo is the fact it will not harden in the can and you are able to store it almost indefinitely. The other amazing quality about this stuff is it hardens and is ready for sanding and paint in under 15 minutes.
Repairing The Porch With Bondo!
 Recently I noticed the columns holding up my covered front porch were showing signs of rotting at the very bottom. Apparently some of the caulking around the top of the column weathered and was allowing moisture in the pole and causing rot.
Recently I noticed the columns holding up my covered front porch were showing signs of rotting at the very bottom. Apparently some of the caulking around the top of the column weathered and was allowing moisture in the pole and causing rot.
Continue reading “BONDO – Its not just for 1970 auto body repair!”








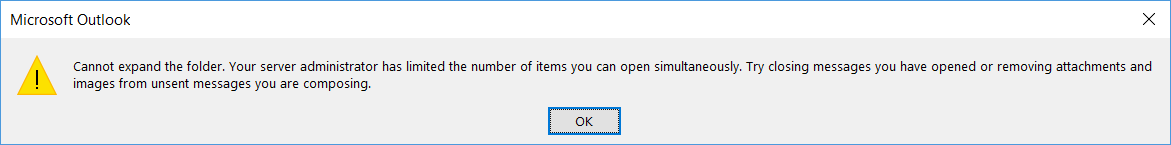
 Last night during a maintenance window I applied my Microsoft updates and rebooted the server. Shortly after reboot I attempted to open Outlook and it failed with a server unavailable error. OWA and ECP both showed BLANK white screens. I began to panic a little because this is probably the IT guys worst nightmare! Working in the industry for over 20 years I put my panic aside and began my standard troubleshooting procedure.
Last night during a maintenance window I applied my Microsoft updates and rebooted the server. Shortly after reboot I attempted to open Outlook and it failed with a server unavailable error. OWA and ECP both showed BLANK white screens. I began to panic a little because this is probably the IT guys worst nightmare! Working in the industry for over 20 years I put my panic aside and began my standard troubleshooting procedure.
 Having a small shop and wearing a lot of hats here in the office tends to create a slew of challenges. Most of the time I have a ton of projects brewing so focusing on one can be difficult at times. My migration to a new Exchange 2016 server will be gradual taking about 2 to 3 weeks to complete. During the initial setup I like to let certain steps “stew” overnight to make sure there are no disruptions. I also like to be sure I have a contingency plan to undo any unforeseen issues.
Having a small shop and wearing a lot of hats here in the office tends to create a slew of challenges. Most of the time I have a ton of projects brewing so focusing on one can be difficult at times. My migration to a new Exchange 2016 server will be gradual taking about 2 to 3 weeks to complete. During the initial setup I like to let certain steps “stew” overnight to make sure there are no disruptions. I also like to be sure I have a contingency plan to undo any unforeseen issues.

 eir mail on my exchange server. When composing a new message the mail is delivered as expected. The fact that this is a new server and the user was migrated just days before led me to believe the issue was on my end.
eir mail on my exchange server. When composing a new message the mail is delivered as expected. The fact that this is a new server and the user was migrated just days before led me to believe the issue was on my end.


